Now Hiring: Are you a driven and motivated 1st Line IT Support Engineer?

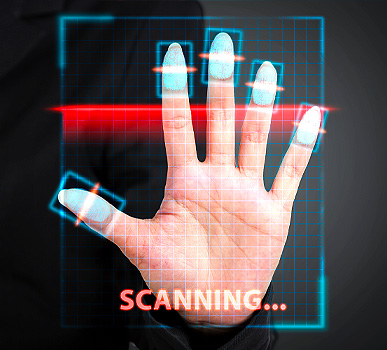
When High Security is of the utmost importance Biometrics plays a very large part in ensuring security. It is already a small part of our world generally with the finger print or facial recognition on our phones.
Biometrics is the physical characteristics of a person with facial recognition, fingerprint matching and retinal scans being the most well-known. However, it can go further with body shapes and natural body scents also being used as identifiers.

There are three basic types of Biometrics, with Morphological being the most commonly used for building or area security, with finger printing being very popular..
Biometric identification can be used effectively to safeguard or work alongside existing systems, to restrict access to buildings, selected areas and rooms, even computers. Once recorded it is encrypted and saved to a data base for future use when accessing a system.

This security system is a very distinct series of actions, especially developed to provide accurate and consistent identification and authentication. These systems follow a precise process to provide security reliability.
1) Data Capture: An individual is scanned to collect the data.
2) Processing: This data is then processed and converted into a data analysed format.
3) Storage: The data is stored as a biometric form template in a database.
4) Matching: When activated the system will attempt to coordinate the data.
5) Outcome: Based on the strength of the match, the system makes a judgement as to deny or allow access.

The incorporation and application of Biometric Security Systems requires careful planning. At Axiom Technology Consulting, we will advise you accordingly, taking into account several factors which would be influenced by your own particular requirements.
